Pengenalan Pola Serangan pada Internet of Thing (IoT) Menggunakan Support Vector Mechine (SVM) dengan Tiga Kernel
DOI:
https://doi.org/10.33998/processor.2023.18.2.1457Keywords:
Machine Learning, Internet of things (IoT), malware, Support Vector Mechine (SVM)Abstract
Internet of things (IoT) technology is very popular these days around the world, with the development of IoT technology raises the impact of security threats and attacks on IoT devices. One of the most is the theft of data and information, one form of threat in IoT is malware. This research uses attacks in the form of bontet to detect attacks on the Internet of Things IoT) and uses Machine Learning to perform data detection of attacks on IoT devices. The method used in this research is Support Vector Mechine (SVM) by comparing three kernels namely Liner, polynominal and Radial Basis Function (RBF). This method is used to determine the level of accuracy in the detection process and compare between kernels. The results obtained are the accuracy value of 0.997 for the liner kernel, meaning that this kernel is able to separate the classes well, while the Polynomial kernel accuracy value of 0.993 is good in separating classes even though the value is smaller than the liner. Meanwhile, the RBF (Radial Basis Function) kernel has an accuracy of 1.0 (100%).
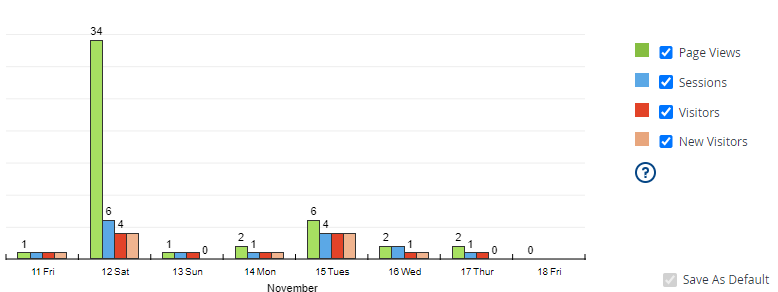
Downloads
References
L. Newcombe, P. Yang, C. Carter, and M. Hanneghan, “Internet of things enabled technologies for behaviour analytics in elderly person care: a survey,” Proc. - 2017 IEEE Int. Conf. Internet Things, IEEE Green Comput. Commun. IEEE Cyber, Phys. Soc. Comput. IEEE Smart Data, iThings-GreenCom-CPSCom-SmartData 2017, vol. 2018-Janua, pp. 863–870, 2018, doi: 10.1109/iThings-GreenCom-CPSCom-SmartData.2017.133.
E. A. Shammar and A. T. Zahary, “The Internet of Things (IoT): a survey of techniques, operating systems, and trends,” Libr. Hi Tech, vol. 38, no. 1, pp. 5–66, Jan. 2020, doi: 10.1108/LHT-12-2018-0200.
S. Kumar, P. Tiwari, and M. Zymbler, “Internet of Things is a revolutionary approach for future technology enhancement: a review,” J. Big Data, vol. 6, no. 1, 2019, doi: 10.1186/s40537-019-0268-2.
E. Bou-Harb and N. Neshenko, “Cyber threat intelligence for the internet of things,” Cyber Threat Intell. Internet Things, pp. 1–89, 2020, doi: 10.1007/978-3-030-45858-4.
P. Anand, Y. Singh, A. Selwal, M. Alazab, S. Tanwar, and N. Kumar, “IoT vulnerability assessment for sustainable computing: Threats, current solutions, and open challenges,” IEEE Access, vol. 8, pp. 168825–168853, 2020, doi: 10.1109/ACCESS.2020.3022842.
H. Wang et al., “An Evolutionary Study of IoT Malware,” IEEE Internet Things J., vol. 8, no. 20, pp. 15422–15440, 2021, doi: 10.1109/JIOT.2021.3063840.
E. M. Karanja, S. Masupe, and J. Mandu, “Internet of Things Malware : A Survey,” Int. J. Comput. Sci. Eng. Surv., vol. 8, no. 3, pp. 1–20, 2017, doi: 10.5121/ijcses.2017.8301.
Z. Liu et al., “An Integrated Architecture for IoT Malware Analysis and Detection BT - IoT as a Service,” 2019, pp. 127–137.
H. Takase, R. Kobayashi, M. Kato, and R. Ohmura, “A prototype implementation and evaluation of the malware detection mechanism for IoT devices using the processor information,” Int. J. Inf. Secur., vol. 19, no. 1, pp. 71–81, 2020, doi: 10.1007/s10207-019-00437-y.
R. Boutaba et al., “A comprehensive survey on machine learning for networking: evolution, applications and research opportunities,” Journal of Internet Services and Applications, vol. 9, no. 1. SpringerOpen, pp. 1–99, 2018. doi: 10.1186/S13174-018-0087-2.
M. Shafiq, X. Yu, A. A. Laghari, L. Yao, N. K. Karn, and F. Abdessamia, “Network Traffic Classification techniques and comparative analysis using Machine Learning algorithms,” 2016 2nd IEEE Int. Conf. Comput. Commun. ICCC 2016 - Proc., pp. 2451–2455, 2017, doi: 10.1109/CompComm.2016.7925139.
L. Kong, G. Huang, K. Wu, Q. Tang, and S. Ye, “Comparison of Internet Traffic Identification on Machine Learning Methods,” in 2018 International Conference on Big Data and Artificial Intelligence (BDAI), Jun. 2018, pp. 38–41. doi: 10.1109/BDAI.2018.8546682.
H. Hindy et al., “A Taxonomy of Network Threats and the Effect of Current Datasets on Intrusion Detection Systems,” IEEE Access, vol. 8, pp. 104650–104675, 2020, doi: 10.1109/ACCESS.2020.3000179.
S. Kakati, D. Chouhan, A. Nag, and S. Panja, “Survey on Recent Malware Detection Techniques for IoT,” Lect. Notes Electr. Eng., vol. 888, no. September, pp. 647–659, 2022, doi: 10.1007/978-981-19-1520-8_53.
A. Wolsey, “The State-of-the-Art in AI-Based Malware Detection Techniques: A Review,” arXiv Prepr. arXiv2210.11239, pp. 1–18, 2022, [Online]. Available: https://arxiv.org/abs/2210.11239%0Ahttps://arxiv.org/pdf/2210.11239
Z. Xu, S. Ray, P. Subramanyan, and S. Malik, “Malware detection using machine learning based analysis of virtual memory access patterns,” Proc. 2017 Des. Autom. Test Eur. DATE 2017, pp. 169–174, 2017, doi: 10.23919/DATE.2017.7926977.
H. Hashemi, A. Azmoodeh, A. Hamzeh, and S. Hashemi, “Graph embedding as a new approach for unknown malware detection,” J. Comput. Virol. Hacking Tech., vol. 13, no. 3, pp. 153–166, 2017, doi: 10.1007/s11416-016-0278-y.
D. Wang, X. Zhang, J. Ming, T. Chen, C. Wang, and W. Niu, “Resetting Your Password Is Vulnerable: A Security Study of Common SMS-Based Authentication in IoT Device,” Wirel. Commun. Mob. Comput., vol. 2018, 2018, doi: 10.1155/2018/7849065.
A. Corum, D. Jenkins, and J. Zheng, “Robust PDF Malware Detection with Image Visualization and Processing Techniques,” in Proceedings - 2019 2nd International Conference on Data Intelligence and Security, ICDIS 2019, 2019, pp. 108–114. doi: 10.1109/ICDIS.2019.00024.
H. Naeem et al., “Malware detection in industrial internet of things based on hybrid image visualization and deep learning model,” Ad Hoc Networks, vol. 105, p. 102154, 2020, doi: 10.1016/j.adhoc.2020.102154.
M. Hirano and R. Kobayashi, “Machine Learning-based Ransomware Detection Using Low-level Memory Access Patterns Obtained From Live-forensic Hypervisor,” in 2022 IEEE International Conference on Cyber Security and Resilience (CSR), 2022, pp. 323–330. doi: 10.1109/CSR54599.2022.9850340.
H. Naeem, B. M. Alshammari, and F. Ullah, “Explainable Artificial Intelligence-Based IoT Device Malware Detection Mechanism Using Image Visualization and Fine-Tuned CNN-Based Transfer Learning Model,” Comput. Intell. Neurosci., vol. 2022, 2022, doi: 10.1155/2022/7671967.
M. Asam et al., “IoT malware detection architecture using a novel channel boosted and squeezed CNN,” Sci. Rep., vol. 12, no. 1, pp. 1–12, 2022, doi: 10.1038/s41598-022-18936-9.
M. Nakahara, N. Okui, Y. Kobayashi, and Y. Miyake, “Malware Detection for IoT Devices using Automatically Generated White List and Isolation Forest,” Int. Conf. Internet Things, Big Data Secur. IoTBDS - Proc., vol. 2021-April, no. IoTBDS, pp. 38–47, 2021, doi: 10.5220/0010394900380047.
C. Y. Wu, T. Ban, S. M. Cheng, B. Sun, and T. Takahashi, “IoT Malware Detection Using Function-Call-Graph Embedding,” 2021 18th Int. Conf. Privacy, Secur. Trust. PST 2021, 2021, doi: 10.1109/PST52912.2021.9647806.
J. Jeon, J. H. Park, and Y. S. Jeong, “Dynamic Analysis for IoT Malware Detection with Convolution Neural Network Model,” IEEE Access, vol. 8, pp. 96899–96911, 2020, doi: 10.1109/ACCESS.2020.2995887.
F. Sharmin et al., “Humidity Based Automated Room Temperature Controller Using IoT,” in 2019 Third International conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), 2019, pp. 226–231. doi: 10.1109/I-SMAC47947.2019.9032624.
A. Indu and S. M. Kumar, “An Approach for Implementing Innovative Weather Monitoring System with DHT11 Sensor and Arduino Uno Tool based on IoT,” in 2022 Sixth International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), 2022, pp. 274–278. doi: 10.1109/I-SMAC55078.2022.9987289.
H. Patel, “Network Traffic Analysis Using Packet Sniffer Pallavi Asrodia *, Hemlata Patel **,” vol. 2, no. 3, pp. 854–856, 2012.
R. Spangler, “Packet sniffer detection with antisniff,” … Wisconsin, Dep. Comput. …, no. May, 2003.
O. n Henry and M. A. Agana, “Intranet Security Using A LAN Packet Sniffer to Monitor Traffic,” pp. 57–68, 2019, doi: 10.5121/csit.2019.90806.
A. Siswanto, A. Syukur, E. A. Kadir, and Suratin, “Network Traffic Monitoring and Analysis Using Packet Sniffer,” in 2019 International Conference on Advanced Communication Technologies and Networking (CommNet), 2019, pp. 1–4. doi: 10.1109/COMMNET.2019.8742369.
R. Alshammari and A. N. Zincir-Heywood, “Can encrypted traffic be identified without port numbers, IP addresses and payload inspection?,” Comput. Networks, vol. 55, no. 6, pp. 1326–1350, 2011, doi: 10.1016/j.comnet.2010.12.002.
A. R. Vasudevan, E. Harshini, and S. Selvakumar, “SSENet-2011: A Network Intrusion Detection System dataset and its comparison with KDD CUP 99 dataset,” Asian Himalayas Int. Conf. Internet, 2011, doi: 10.1109/AHICI.2011.6113948.
M. Y. Su, “Real-time anomaly detection systems for Denial-of-Service attacks by weighted k-nearest-neighbor classifiers,” Expert Syst. Appl., vol. 38, no. 4, pp. 3492–3498, 2011, doi: 10.1016/j.eswa.2010.08.137.
S. Hao, J. Hu, S. Liu, T. Song, J. Guo, and S. Liu, “Improved SVM method for internet traffic classification based on feature weight learning,” ICCAIS 2015 - 4th Int. Conf. Control. Autom. Inf. Sci., pp. 102–106, 2015, doi: 10.1109/ICCAIS.2015.7338641.
R. G. Azhari, V. Suryani, R. R. Pahlevi, and A. A. Wardana, “The Detection of Mirai Botnet Attack on the Internet of Things (IoT) Device Using Support Vector Machine (SVM) Model,” in 2022 10th International Conference on Information and Communication Technology (ICoICT), 2022, pp. 397–401. doi: 10.1109/ICoICT55009.2022.9914830.
S. Mishra, “Detection and mitigation of attacks in SDN-based IoT network using SVM,” Int. J. Comput. Appl. Technol., vol. 65, no. 3, pp. 270–281, Jan. 2021, doi: 10.1504/IJCAT.2021.116009.